This is the first in the series of three articles I will be publishing over the next two weeks. In my Big Three List, AI and blockchain, the two media darlings of the day, play important albeit supporting roles.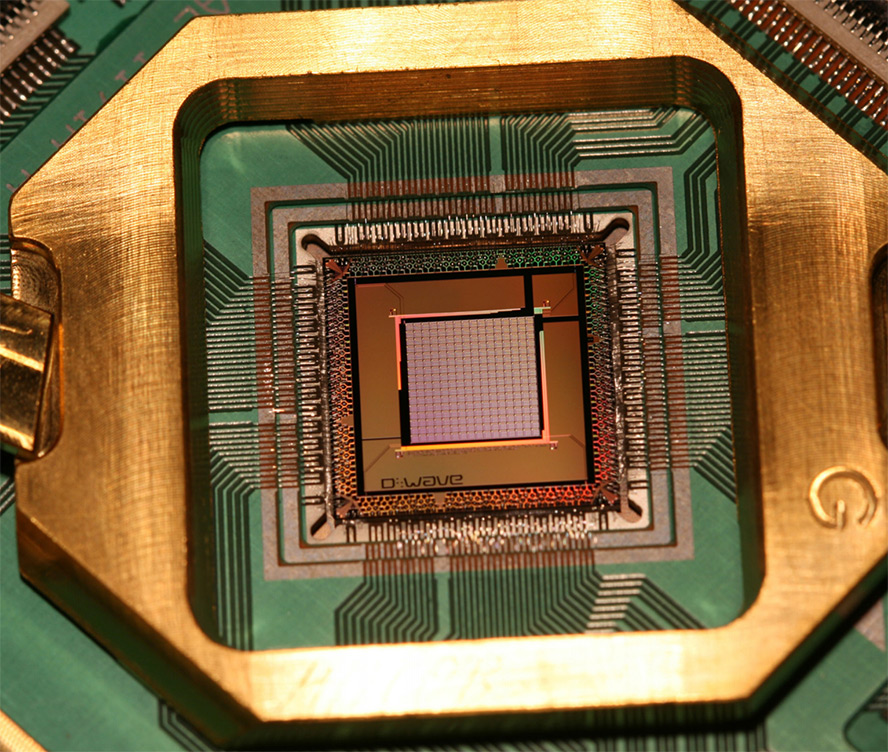
Today a number of well-known players are engaged in building and refining quantum computer architecture. There is the D-Wave’s D-Wave 2000Q System (in this post I used a photo of D-Wave Quantum Processor), Microsoft’s Station Q, and IBM’s Q—just to name a few. The specifics of each system are beyond the scope of this article, but what is important is that the computing power of a quantum computer is many orders of magnitude greater than that of the fastest conventional systems. Turbocharged with such incredible computing power, any technology that relies on computing muscle—from AI and machine learning to cryptocurrency mining and cryptography—will leapfrog into a new state of being. The fundamental growth in capabilities made possible by quantum computing power will be far greater than the effect that moving from 56.6k dial-ups to high-speed fiber optics lines has had on data communications and the services they enable.
Quantum computing resembles nuclear energy in terms of the magnitude of positive (enablement) and negative (disruptive and destructive) power it wields with the choice of the application determined by the motivations of its users. One commonly cited application of quantum computing power is to break encryption algorithms used today to secure data and enable encryption-based technologies, such as blockchain. The race is on to develop new post-quantum encryption algorithms that can withstand the quantum-powered brute-force attacks. Blockchain-specific research is also in progress to quantum-proof its underlying cryptography.
Based on my review of the current literature, at least from a layman’s perspective, it is difficult to determine to what degree the advancements in quantum computing have already endangered the integrity of existing “strong encryption” protocols. Such uncertainty, which has very clear political and strategic implications, is only to be expected. This is where history lessons can be very instructive. For example, breaking Enigma encryption during the World War II, the story of which was retold and popularized in 2014 movie “The Imitation Game,” has not been disclosed until the 1970s, decades after the fact, to benefit those whose adversaries continued to encrypt their sensitive data using the compromised technology. I expect that quantum-powered decryption efforts will follow a similar disclosure timeline, unless, of course, a group of brilliant teenagers figures out how to build a makeshift quantum computer in their garage, breaks the AES-256 and/or RSA 4096-bit encryption to test the system, and posts the results on Facebook.
