Our Approach
In our work, we adopted the tenets of Agile Manifesto to prioritize delivery of business value over scrupulous documentation. We value trust and relationships with our clients over perfect processes and sophisticated tools*. We prefer to engage in mutually beneficial collaboration over contract negotiation. We value agility and embrace change—the key element of fulfilling our promise to you and our mission to SECURE YOUR GROWTH™.
We are equally comfortable with completing our assignments interactively, working side-by-side with your team, as well as acting completely independently within the scope of the assigned responsibilities. We quickly and easily adapt to your organizational culture and processes.
*Albert Einstein said that “The perfection of means and the confusion of ends seems to be our problem.” At ZHUK, we take his astute warning to heart.
Technology Governance
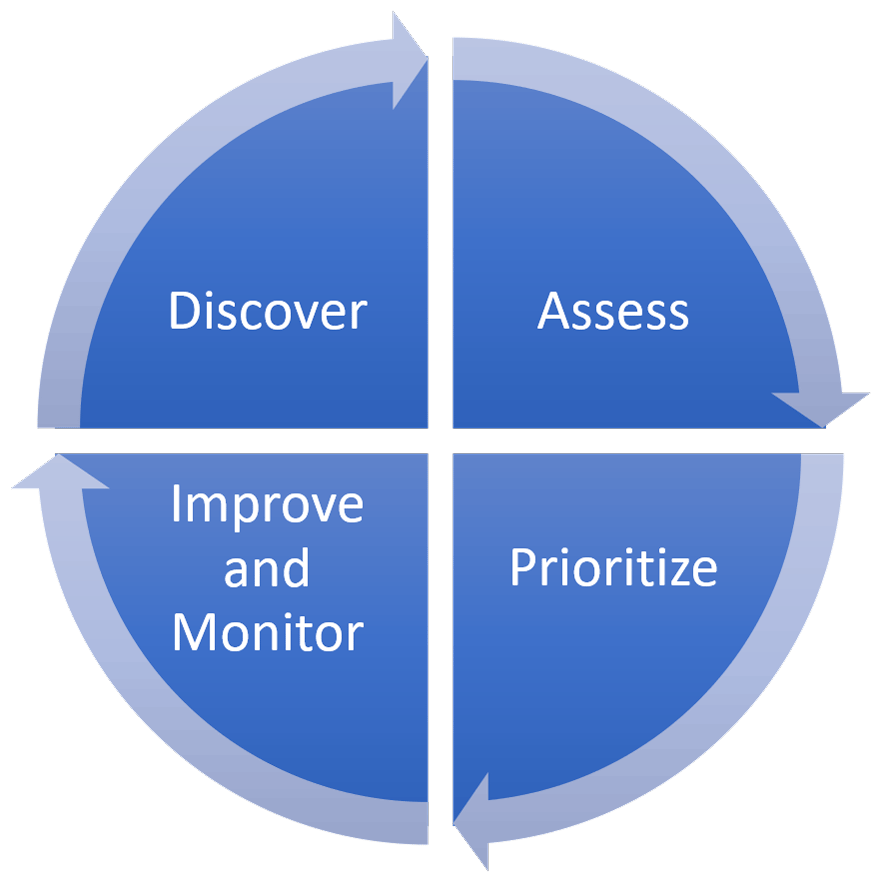
According to ISACA, “The objective of any governance system is to enable organizations to create value for their stakeholders or to promote value creation.” The IT governance process is a never-ending cycle informed by four fundamental questions:
- Are we doing the right things?
- Are we doing them right?
- Are we doing them well?
- Are we getting the desired benefits?
Sound IT governance practices can be notoriously difficult to implement, especially when communications channels are broken and key stakeholder engagement is lacking. Let us help you at every step of your IT governance definition and improvement journey. Our work on business value shaping, value harvesting, and value maximization has helped hundreds of organizations across the world to improve their IT resource allocation and value realization.
Our IT governance consultants are Certified in Governance of Enterprise IT (CGEIT).
IT Risk Management
Hardly any leading organization achieved its industry position without taking calculated risks, yet it is very common among the information security and IT risk professionals to take a one-sided negative only view on risk. This lopsided view is due, in part, to the conflicting definitions of risk coming from such authoritative sources as ISO/IEC 27005:2011 standard, which defines information security risk as “the potential that a given threat will exploit vulnerabilities of an asset or group of assets and thereby cause harm to the organization.” On the other hand, the latest editions of ISO 31000:2018 and COSO ERM Framework (2017) guidance underscore the dual nature of risk, which can lead to positive as well as negative outcomes.
Allow us to help you navigate through the often confusing and sometimes outright conflicting guidance on building and maintaining a stellar risk management program. We have years of experience in designing and implementing strategically focused Enterprise Risk Management (ERM) programs based on the latest international (ISO) and national (COSO, NIST) frameworks.
Our IT risk management consultants are Certified in Risk and Information Systems Control (CRISC).
Audit and Compliance
Whether you are a mature enterprise or a nimble FinTech startup, your organization is subject to numerous regulatory and industry standards compliance requirements. Leverage our extensive Fortune 100 and startup expertise to help you with your compliance needs and free up your precious resources to focus on moving your business forward. Allow us to assist you with passing compliance audits and improving your compliance standing.
- 3rd-Party Independent Compliance Assessments
- Certified Cybersecurity Audits
- Compliance Management System (CMS) Assessment and Architecture
- PCI Compliance Reviews and Attestation
- Infrastructure Architecture Compliance Reviews
- Preparation for and Assistance with Regulatory Audits (ISO, SOC, and NIST)
- Preparation for and Assistance with Passing Information Security and IT Governance Audits
Our compliance consultants are Certified in Risk and Information Systems Control (CRISC) and Certified Information Security Managers (CISM).
Information Security
Information security threats range from curious
- Secure Architecture Design and SSDLC
- Information Security Program Development (ISO 27000, NIST)
- Information Security Assessments and Penetration Testing
- COB and Disaster Recovery Planning
- Information Security Breach Recovery and Investigations
Our information security consultants are Certified Information Systems Security Professionals (CISSP) and Certified Information Security Managers (CISM).
Service Management
Whether you just embarked on your first IT service management journey or are looking for ways to improve your sophisticated service catalog, our knowledgeable consultants will provide the expertise and assistance you need to be successful in your undertaking.
We have extensive experience in using IT service management (ITIL) and Business Relationship Management (BRM) guidance to break down communication barriers among various internal IT organizations and services. We will work with your IT leadership to get them started on a collaborative journey of continuous service improvement and business value maximization.
Our IT service management consultants are ITIL Expert and Business Relationship Management Professional (BRMP) certified.
