The Future of Computing Infrastructure in Two Easy Steps
The Future of Computing Infrastructure in Two Easy Steps TECHNOLOGY & BUSINESS Aleksandr Zhuk October 21, 2018 In the early days of automobile, to operate a car a driver had to be an engineer intimately familiar with the structure and principles of...
Quantum Zero Trust Model: The Future of Secure Systems Architecture
Quantum mechanics offers numerous mysteries to ponder for laypeople and physicists alike, but none of these mysteries is more popular among the general public as the famous Schrödinger's cat experiment. Conceived by Austrian physicist Erwin Schrödinger in 1935, the...
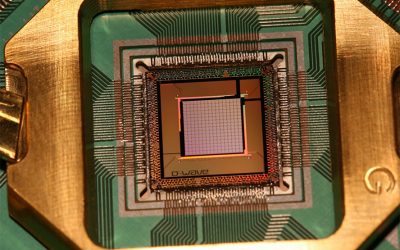
Quantum Computing and Encryption. Three Technologies Defining the Future of Information Security and Business – Part I.
This is the first in the series of three articles I will be publishing over the next two weeks. In my Big Three List, AI and blockchain, the two media darlings of the day, play important albeit supporting roles. Today a number of well-known players are engaged in...